Alwinco’s methodology and the crime triangle.
Security Risk Assessment—Over the years, Alwinco has developed an original and unmatched approach to crime prevention and security. Our experience has enabled us to formulate a unique method that has consistently proven successful and sets us apart from many other security companies. To fully grasp our methodology and the principles behind our Security Risk Assessment, it is essential to understand the concept of opportunity, a crucial factor in both crime and effective crime prevention.
‘Opportunity’ refers to the circumstances and conditions that create a favorable environment for crime to occur.
Criminals often seek situations where they can commit crimes with minimal risk of detection or being captured. By understanding and reducing these opportunities, we can effectively prevent crime.
At Alwinco, we believe that a proactive approach to security is key to preventing crime. Rather than solely relying on reactive measures such as alarms or surveillance cameras, we focus on eliminating or minimizing the opportunities for crime to take place. This strategy has been highly successful in reducing crime rates.
Our Security Risk Assessment methodology
involves identifying and analyzing potential vulnerabilities and weaknesses within a specific environment. We assess factors such as physical layout, access control systems, lighting, and security procedures to identify areas where criminals might find opportunities. By addressing these vulnerabilities, we create a more secure environment that deters criminal activity and makes it difficult for criminals to execute their intentions.
Through our unique approach and methodology,
we aim not only to detect and respond to crime but also to prevent it from occurring in the first place. By reducing opportunities, we decrease the likelihood of criminal incidents and create safer communities and environments for individuals and organizations. Our commitment to understanding and addressing the role of opportunity in crime prevention is what distinguishes us from many other security companies. We believe that by focusing on this critical aspect, we can significantly reduce crime rates and enhance overall security.
The crime triangle.
When we were in school, many of us learned about the Fire Triangle. We were taught that for a fire to burn, three elements are required: heat, fuel, and oxygen. If any one of these components are removed, a fire cannot occur.
Crime, like fire, requires three components to occur:
- Desire
- Ability
- Opportunity

The crime triangle AI
All 3 of these components are directly related to criminal activity.
By removing just one element, you can effectively prevent a crime from occurring.

To better understand the crime triangle, consider the well-known iceberg analogy. Just as the tip of an iceberg is only a small part of a much larger mass hidden beneath the water, the visible signs of criminal activity often represent only a fraction of a more significant and potentially damaging situation. Remember what happened to the Titanic?
The tip of the iceberg is typically the smallest part of a much larger and more dangerous problem. Many people mistakenly believe that if something is not immediately visible, it does not exist. When the Titanic encountered the iceberg, the visible tip caused minimal damage, while the much larger, hidden portion of the iceberg led to the ship’s destruction and the tragic loss of many lives.
In today’s world, we try to protect what is like the Titanic, while the crime triangle acts like the iceberg threatening it.
Often, people overlook the invisible part of the iceberg, opportunity, and only realize it too late as the true cause of the problem, much like the hidden part of the iceberg that sank the Titanic. The same applies to our approach to crime today. We often mistakenly focus on aspects beyond our control, such as desire and ability, rather than concentrating on what we can control: opportunity. The desire to commit a crime is an inherent trait, shaped by an individual’s mindset, past experiences, upbringing, belief system, ethics, and personal situation. These are factors over which we have no control.
Similarly, the criminal’s ability to commit a crime involves physical strength, capabilities, and mental capacity.
While we can attempt to hinder the criminal by making it more challenging to commit the crime, such as by increasing wall heights, strengthening burglar bars, or implementing more sophisticated security systems—these measures might only discourage the criminal temporarily. If the criminal is determined, they may still find a way around these obstacles.
The most significant and often overlooked factor is opportunity. The key to effective crime prevention lies in removing this crucial aspect.
Opportunities range from observing a predictable schedule, having tools on hand, poorly managed security systems, and transporting weapons into a facility undetected. The possibilities are endless.
Most criminals are inherently opportunistic. However, we must not overlook those lawbreakers who meticulously plan their attacks.
Consequently, by removing these opportunities, we can eliminate the threat of most crimes. It is crucial for any VIP to be cautious and avoid providing criminals with an opportunity to target them. This can be done by refraining from sharing excessive personal information on social media and varying their daily routes. It is advisable to avoid sitting near windows or in direct line of sight when the door is open. In the past, people always emphasized avoiding being in the line of fire of an attacker.
Written by Andre Mundell, security risk consultant at Alwinco. # Security Risk Assessment
Should you wish to learn more about our services offered or want more information on security risk assessments, please send us an email or kindly visit our website security meetings and subscribe to our Newsletter.
Furthermore, in addition to other major cities in Gauteng, our security risk assessment services are accessible in Arcadia, Bloemfontein, Bluff, Johannesburg, Erand Gardens, and Midrand.
Which 20% of your employees are considered expendable?
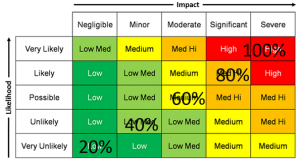
What represents an acceptable risk to you? Security risk assessment levels— If you want to draw a distinction between acceptable risk and unacceptable risk, perhaps you need to consider what security means to you. Health & Safety has taught us that there is an “acceptable risk,” and while that may be true in the … Continue reading